Security Immersive Training System (SITS)
SITS Capabilities
- Force on Force, Counterterrorism, Direct Action Engagement
- Execution of Security Team Tactics, Techniques and Procedures
- Security Planning Team Course of Action Development, Execution and Assessment
- Facility and Critical Asset Vulnerability
- Protection Planning and Assessment
- Crisis Response Planning and Assessment
- Mission Rehearsal
- Scenario Development, Performance Feedback and Lessons Learned
A new system being developed bythe Cubic Innovation and Technology Center integrates software and technologies to provide what is known as “live, virtual and constructive” (LVC) training in one portable and expandable package.
Called the Security Immersive Training System (SITS), the concept calls for a core package for providing constructive training that can be expanded to incorporate virtual and live training, all at the same time. For the project, Cubic is partnering with Albuquerque-based RhinoCorps, which makes a constructive simulation software tool called Simajin. SITS will also incorporate a powerful computer gaming engine and 3-D terrain software similar to Google Earth. The core of SITS will be made from commercial-off-the-shelf hardware and will be designed so that existing Cubic products — the COMBATREDI virtual-reality trainer, the Multiple Integrated Laser EngagementSystem – Individual WeaponsSystem (MILES IWS) and the Initial–Homestation Instrumentation Training System (I-HITS) — can beintegrated with it.
LVC training is a combination of three categories:
Live, the old standby, istraining in the real world using real people and actual equipment, including soldiers and combat vehicles equipped with laser weapon simulators such as Cubic's MILES gear. It has a disadvantage of being expensive and hard on equipment, but provides the most “fidelity” — a term that describes the realism of training.
Virtual uses software andcomputer hardware, such as flight simulators or COMBATREDI, allowing humans to interact with a virtual environment, as when playing a computer video game. It is relatively inexpensive, but lacks some of the fidelity of live training.
Constructive training uses simulated people acting out computerized scenarios in simulated environments. Humans provide input, such as the location of equipment, barriers and forces, but the outcome is determined by the simulation software. Constructive training allows scenarios to be easily repeated thousands of times with subtle changes, but has the least fidelity of the three.
Finding the proper mix of these three categories to provide training that is worthwhile yet cost-effective is the Holy Grail for military and security planners these days.
The concept for SITS emerged when Cubic officials were brain stormingthe kinds of threats and potential threats the military and security forces are training for today.
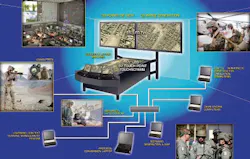
SITS will consist of a core system of two large flat-screen TVs, a touch-screen LCD display and computer laptops running the gaming, terrain and constructive-simulation software. The right screen, for example, could display a high-resolution 3-D overhead view of the terrain, with avatars for vehicles and people playing out the constructive simulation. The left screen, powered by the gaming engine, could display a realistic perspective from the view of a soldier at a sniper post watching the action unfold.
The touch screen would allow planners to manipulate various elements in the scenario to see how that affects the outcome. One would allow, say, a squad of a dozen Marines wearing COMBATREDI equipment, and training in a 3-D virtual environment, to be incorporated into the constructive training, appearingon the SITS screen as two dimensional elements of the scenario. Or, using MILESIWS and I-HITS gear, soldiers participating in live training could also be added to the mix.
Security planners could manipulate numerous elements, such as entry points for the terrorists, explosions, the location of direct-action teams and snipers, emergency routes, traffic, communications and even the reaction of the crowd. Running the simulation again and again would help determine the best ways for security forces to set up for and respond to a variety of attacks. Security training exercises and support and threat analysis are other potential uses.